The MikroTik Security Guide and Networking with MikroTik: MTCNA Study Guide by Tyler Hart are available in paperback and Kindle!
Since the release of RouterOS 6.29.1 and the introduction of the new FastTrack feature, there's a bit of confusion out there about how to implement FastTrack rules in the firewall. With later releases of RouterOS the FastTrack feature has started working on more interfaces, including VLANs, so it's even more important to learn this feature and implement it properly. We want forwarded traffic across the router to be marked for FastTrack in the firewall, but we still have to Accept that same traffic as well. Without both of these rules it won't work, and you won't reap the performance benefits.
If you're not familiar with firewall rule and chain basics take a look at the Mikrotik firewall article that breaks them down.
FastTrack has been shown to reduce CPU utilization by quite a bit, in some cases over 10% when traffic volume is high. It operates on the premise that if you've already checked one packet in a stream against the firewall and allowed it, why do you need to check all the other packets in the rest of the stream? In terms of overall efficiency this is big, especially if you have more than just a few firewall rules to evaluate traffic against.
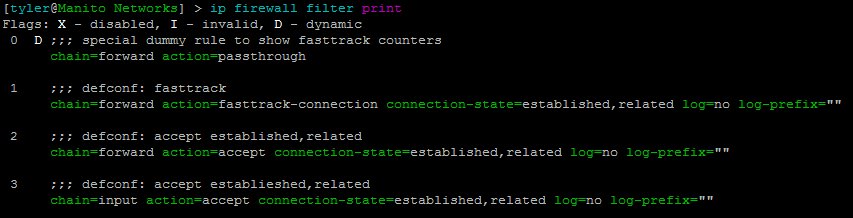
You can see rule number 3 in the screenshot below:
Mikrotik firewall rules with FastTrack configured
Under the IP > Settings menu in Winbox you can also see a counter of all total packets that have been marked for Fast Track:
Mikrotik FastTrack packet counter
Here are the firewall rules currently in use on one of my SOHO devices that take advantage of FastTrack:
/ip firewall address-list add address=192.168.0.0/16 list=Bogon add address=10.0.0.0/8 list=Bogon add address=172.16.0.0/12 list=Bogon add address=127.0.0.0/8 list=Bogon add address=0.0.0.0/8 list=Bogon add address=169.254.0.0/16 list=Bogon /ip firewall filter add chain=input comment="Accept Established / Related Input" connection-state=established,related add chain=input comment="Allow Management Input - 192.168.88.0/24" src-address=192.168.88.0/24 add action=drop chain=input comment="Drop Input" log-prefix="Input Drop" add action=fasttrack-connection chain=forward comment=\ "FastTrack Established / Related Forward" connection-state=\ established,related add chain=forward comment="Accept Established / Related Forward" \ connection-state=established,related add chain=forward comment="Allow forward traffic LAN >> WAN" out-interface=ether1-gateway src-address=192.168.88.0/24 add action=drop chain=forward comment="Drop Bogon Forward >> Ether1" in-interface=ether1-gateway log=yes log-prefix="Bogon Forward Drop" src-address-list=Bogon add action=drop chain=forward comment="Drop Forward"
The two rules above in bold are where the rubber meets the road, and they are both needed to make it work. These same rules can be applied in an enterprise network environment and tweaked accordingly. Enjoy the performance boost!