MikroTik DDoS Attack Mitigation
The MikroTik Security Guide and Networking with MikroTik: MTCNA Study Guide by Tyler Hart are available in paperback and Kindle!
Preface
Being attacked sucks and we hate it. Done. Here's a solution for mitigating an attack. This will not block large-scale DDoS attacks which requires coordination with upstream providers and possibly additional hardware capabilities.
Threat Address List
A DDoS attack comes from many sources and it's a heck of a lot easier to block connections using an Address List. The alternative is making a ton of standalone rules and we hate that too. Identify the malicious traffic sources (e.g. 1.1.1.1 and 2.2.2.2) and create an Address list:
/ip firewall address-list
add address=1.1.1.1 list=Blackhole
add address=2.2.2.2 list=BlackholePrerouting Filter Rule
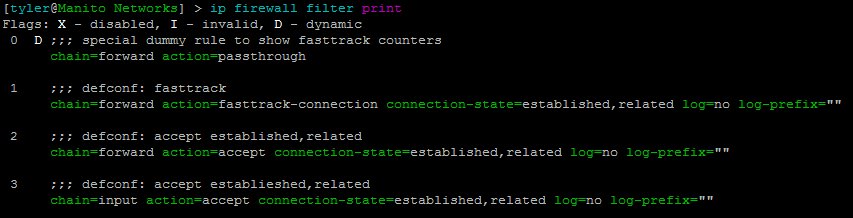
Check out the MikroTik RouterOS packet flow diagram first before going any further if you aren't familiar with the packet flow. To endure an attack we want to filter / drop traffic as close to the source as possible. The further a router has to process bad traffic the more strain it puts on the device. The Prerouting process is a great place to block traffic on the device itself if you don't have blackholing configured with your upstream providers.
Create a Prerouting filter rule using the Blackhole address list we just created and the Drop action:
/ip firewall raw
add chain=prerouting src-address-list=Blackhole action=drop place-before=0As new malicious IP addresses are detected just add them to the Address List.
Fin.