P2P Filtering
The MikroTik Security Guide and Networking with MikroTik: MTCNA Study Guide by Tyler Hart are available in paperback and Kindle!
Preface
Limiting Peer-to-Peer (P2P) network traffic is important for businesses and other network operators for a couple reasons, mainly risk management and bandwidth conservation.
Navigation
Risk Considerations with P2P
Risk management in terms of P2P has multiple facets - stopping illicit material downloads, preventing sensitive data exfiltration from a network. Some viruses use P2P protocols to communicate with botnet operator Command & Control (C&C) servers.
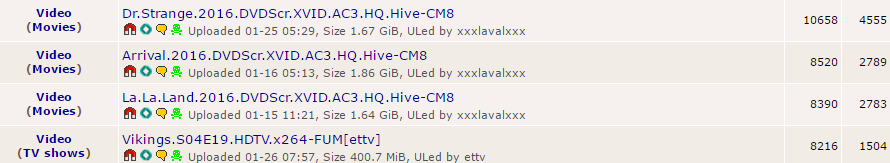
From a legal perspective there is also the risk of being labelled a "copyright infringer" due to your public IP being flagged as part of the download / upload pool for a pirated movie or music album. This brings with it a separate set of non-technical challenges, and possible action on the part of your service provider to terminate services.
Possible Benefits of P2P
While being aware of the risks of P2P, also bear in mind possible benefits. Some operating systems use P2P protocols to distribute software patches and updates within the local network between clients, saving bandwidth and processing load on central servers. Some antivirus vendors also use P2P to distribute large anti-virus signature updates between agents, reducing bandwidth consumption considerably. Many AAA-title games use P2P to distribute patches and content updates, so blocking P2P on a WISP network or small ISP could have an impact on customers.
Carefully consider the impact of blocking P2P in your networks before moving forward.
Blocking P2P in Firewalls
With Mikrotik's P2P firewall functionality it's very easy to both filter P2P traffic and add the hosts that are creating the traffic to an address list, allowing for some accountability.
Mikrotik P2P Firewall Rules
Here are the two firewall commands that detect P2P traffic, add the offending host to a dynamic address list, and then block traffic from hosts on that list:
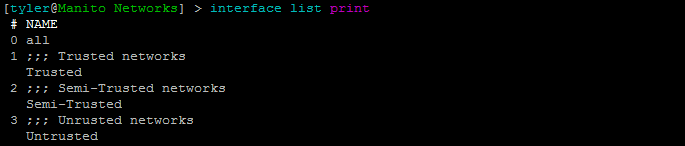
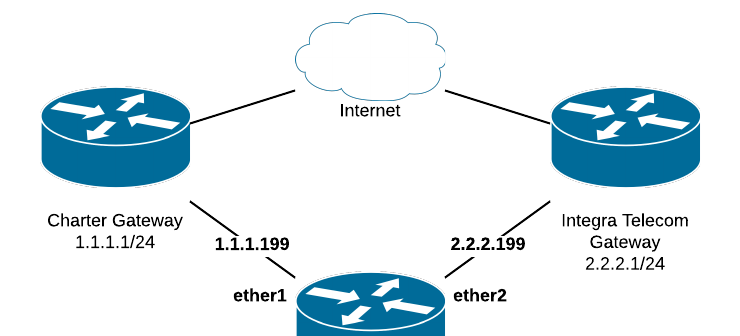
/ip firewall filter add action=add-src-to-address-list address-list=P2P address-list-timeout=30m chain=forward comment="Add P2P hosts to address list" out-interface=ether1-gateway p2p=all-p2p
/ip firewall filter add action=drop chain=forward comment="Drop traffic from P2P hosts" out-interface=ether1-gateway src-address-list=P2PRule Breakdown
Let's break down each rule in turn. The first rule in the foward chain (chain=forward, data going through the router) and being routed out the WAN interface (out-interface=ether1-gateway) checks for P2P traffic (p2p=all-p2p). When P2P traffic is found it triggers action=add-src-to-address-list and adds the offending host's IP to the dynamic "P2P" list (address-list=P2P). It adds the host IP to the list for 30 minutes (address-list-timeout=30m), so that traffic isn't blocked forever by the next rule in case of a false-positive. If it isn't a false positive the host will be re-added after it falls off the address list if more P2P traffic happens.
The second rule drops (action=drop) all traffic from hosts on the P2P address list (src-address-list=P2P) going out the WAN port (out-interface=ether1-gateway) to the Internet. If you need more information about firewall actions, rules, etc see the Mikrotik Firewall write-up. It will continue dropping traffic until the host falls off the address list after 30 minutes. Once on the list whomever is using this host can't access the Internet, but they will still be able to reach internal network resources like servers and printers. By tweaking the second firewall rule it's possible to limit network traffic further.
Additional Steps
Adding a third network rule could allow for a Syslog message to be sent, if Network Admins are monitoring Syslog messages and a Syslog log action has been set up. Helpdesk staff can check the dynamic P2P address list to see what hosts have tripped the P2P rules and begin to remediate the issue.